netclaw init
First-run wizard. Configures your provider, security policy, channels, identity, skills, and network exposure in one pass, then starts the daemon.
netclaw initOptions
Section titled “Options”| Flag | Description | Default |
|---|---|---|
| (none) | Launch the interactive wizard | — |
Before you begin
Section titled “Before you begin”Have these ready before starting:
- LLM provider credentials — an OpenRouter API key (easiest) or Ollama installed locally
- Slack tokens (if using Slack) — Bot Token (
xoxb-...) + App Token (xapp-...). See the Slack quickstart - Discord bot token (if using Discord) — from the Discord developer portal
No other dependencies needed.
Wizard steps
Section titled “Wizard steps”The wizard adapts to your choices — steps get skipped based on your security posture and feature selections.
1. LLM Provider
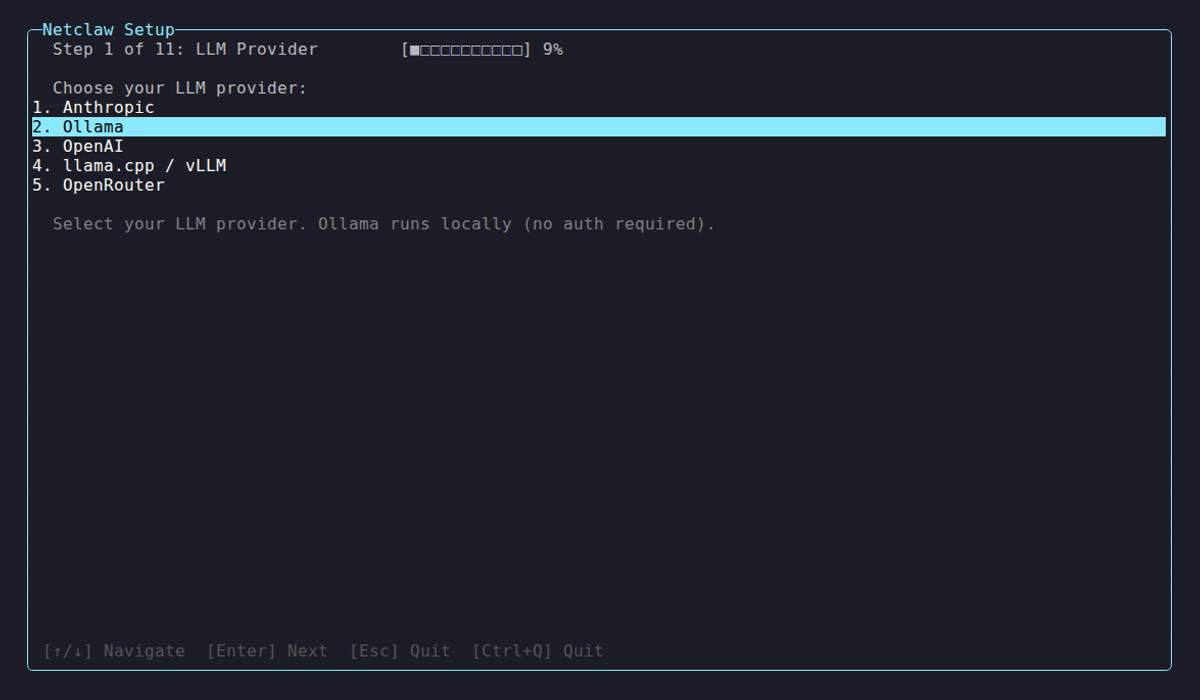
Section titled “1. LLM Provider”Pick a provider, enter credentials, select a model.
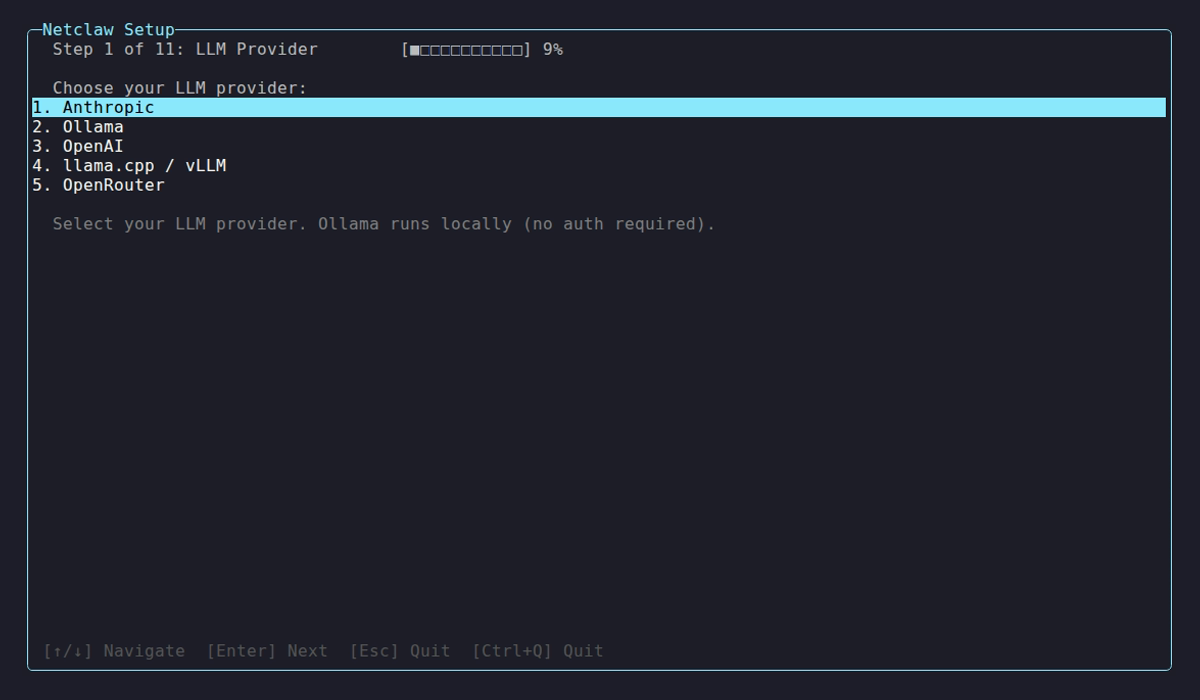
Netclaw supports many providers out of the box — pick one to start with here, and use netclaw provider to add more later. Self-hosted providers like Ollama need an endpoint URL:
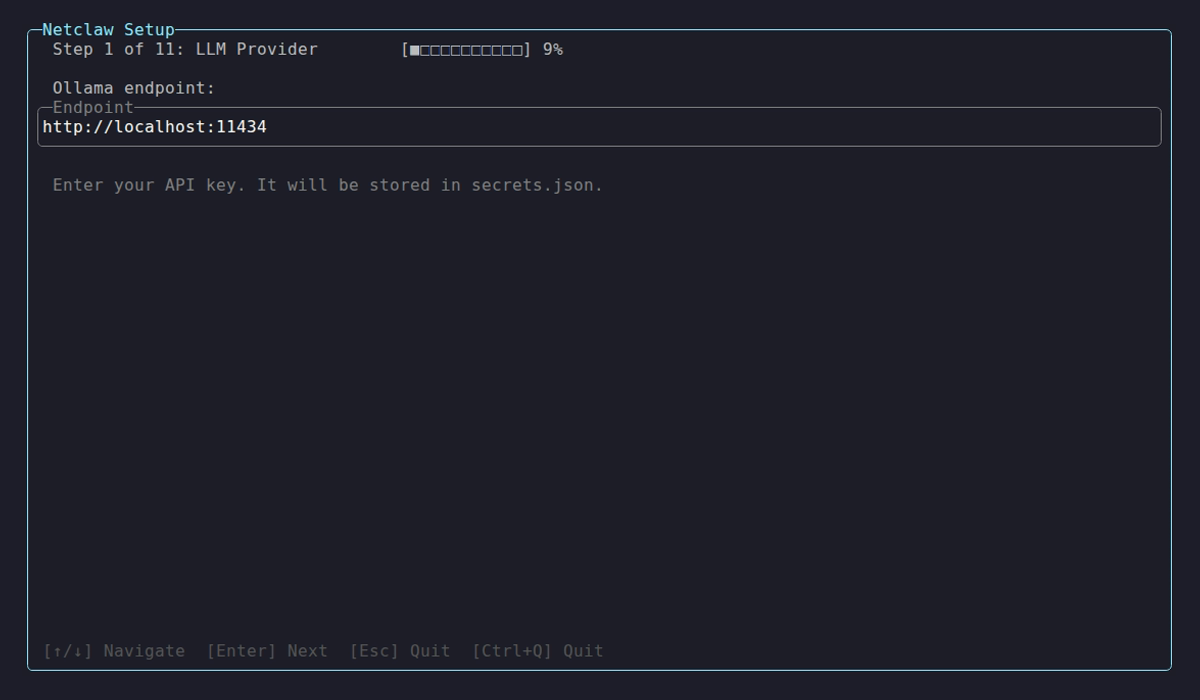
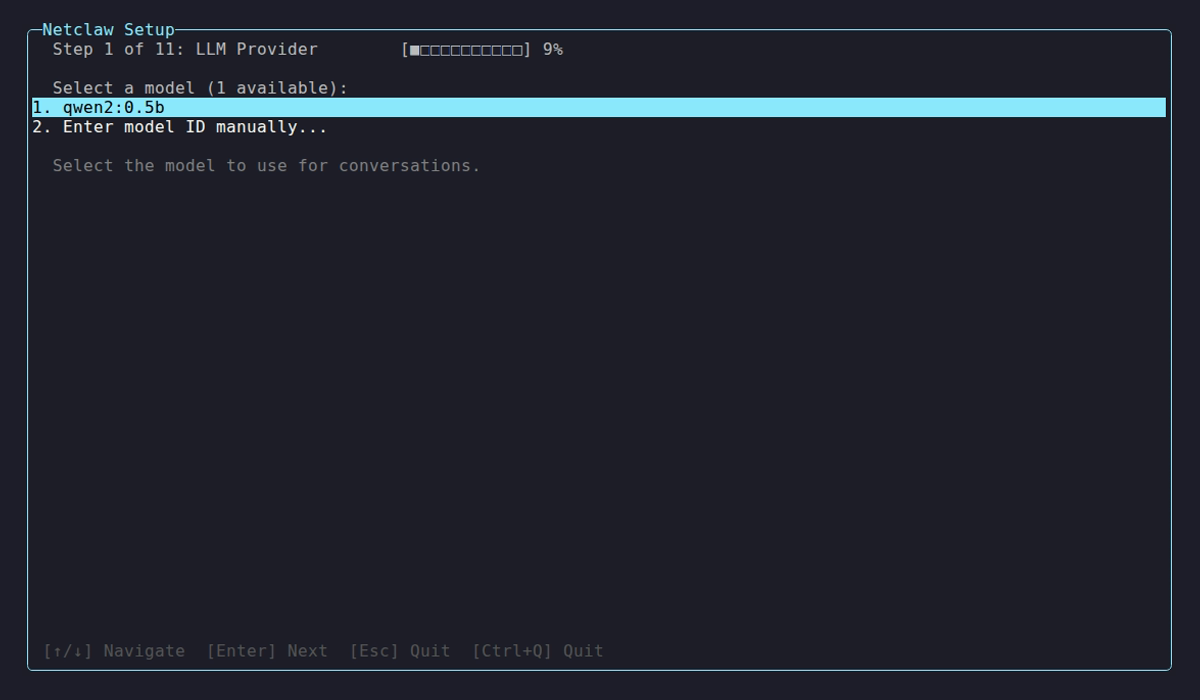
Once credentials pass a connectivity check, you pick a default model:
2. Security posture
Section titled “2. Security posture”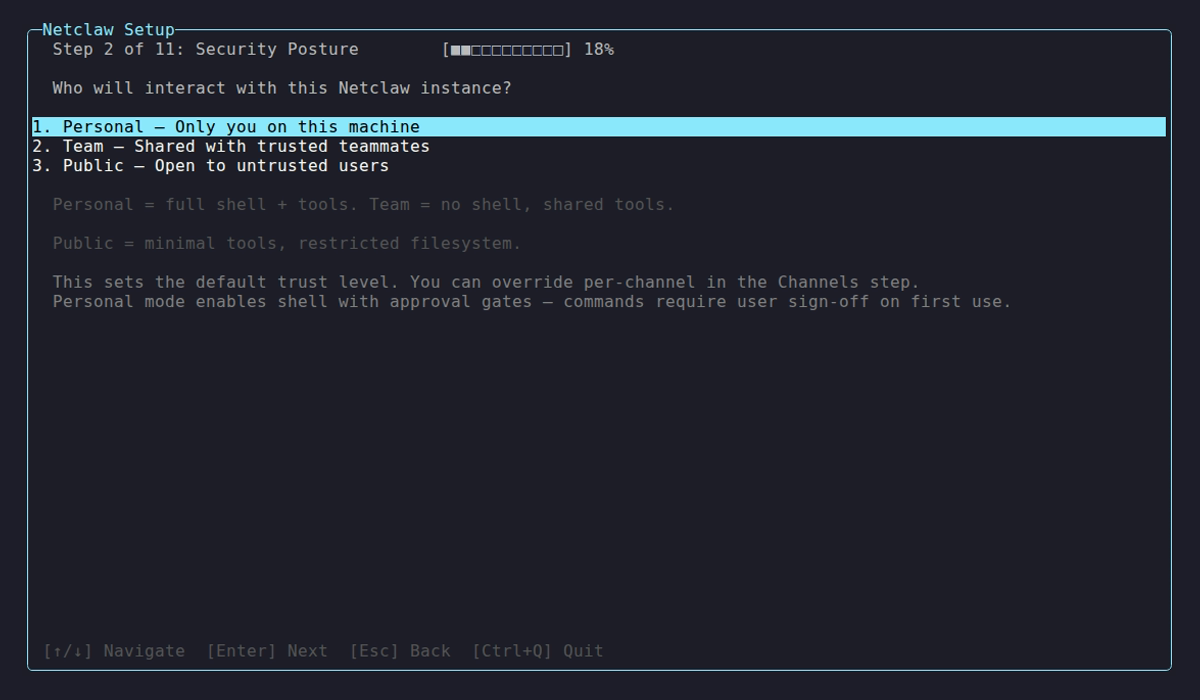
| Posture | Trust Level | Shell Access |
|---|---|---|
| Personal | Single-user, high trust | Enabled with approval gates |
| Team | Multi-user, medium trust | Off by default |
| Public | Untrusted users, low trust | Off |
Every new shell command needs your sign-off the first time. You can override per-channel later.
3. Feature selection
Section titled “3. Feature selection”Enable or disable memory, search, skills, scheduling, sub-agents, and webhooks. Skipped in Personal mode (everything on by default).
4. Channels
Section titled “4. Channels”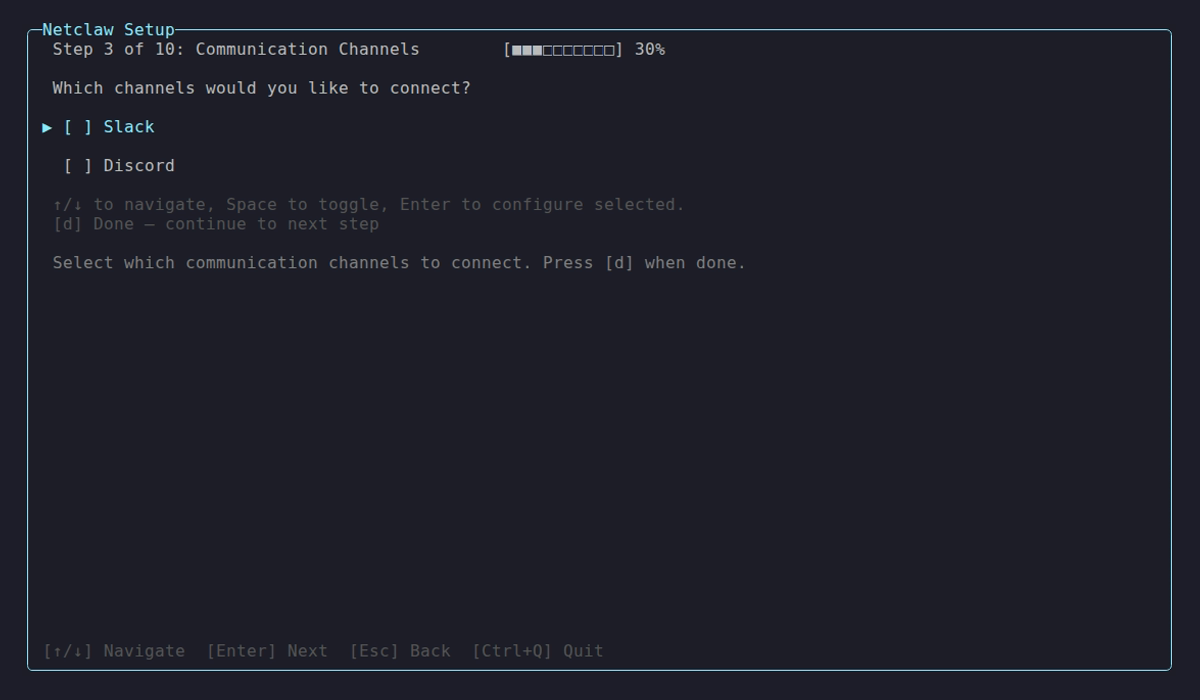
Slack, Discord, or both. Each one opens a sub-step for tokens and workspace config.
Slack needs a Bot Token (xoxb-...) and App Token (xapp-...) for Socket Mode. It tests connectivity before moving on.
5. Web search
Section titled “5. Web search”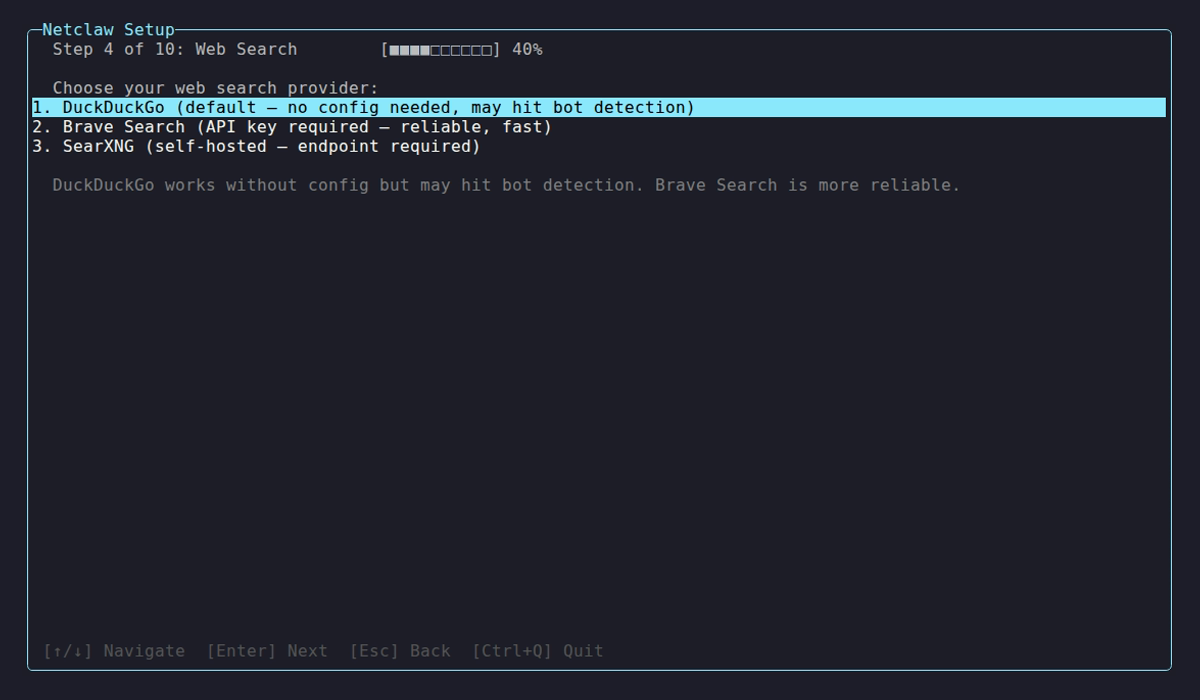
Enable web search so netclaw can pull live results during conversations.
6. Browser automation
Section titled “6. Browser automation”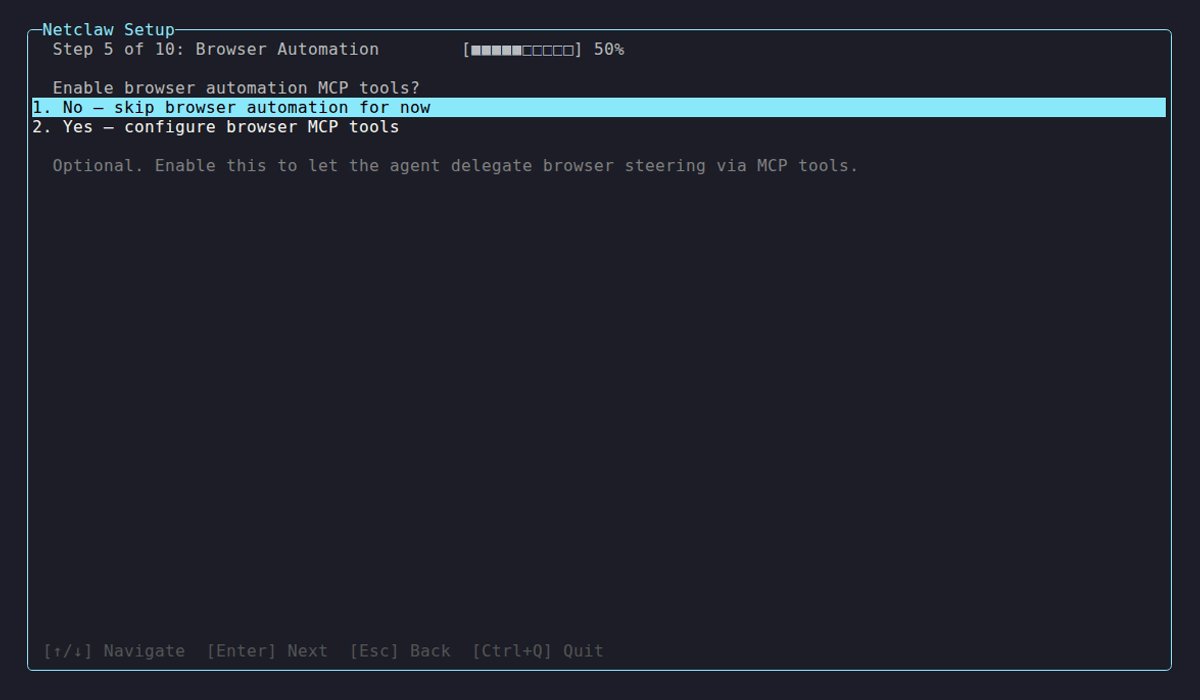
Activate browser automation — page fetching, screenshots, form interaction.
7. Identity
Section titled “7. Identity”
The owner identity determines who gets operator-level access.

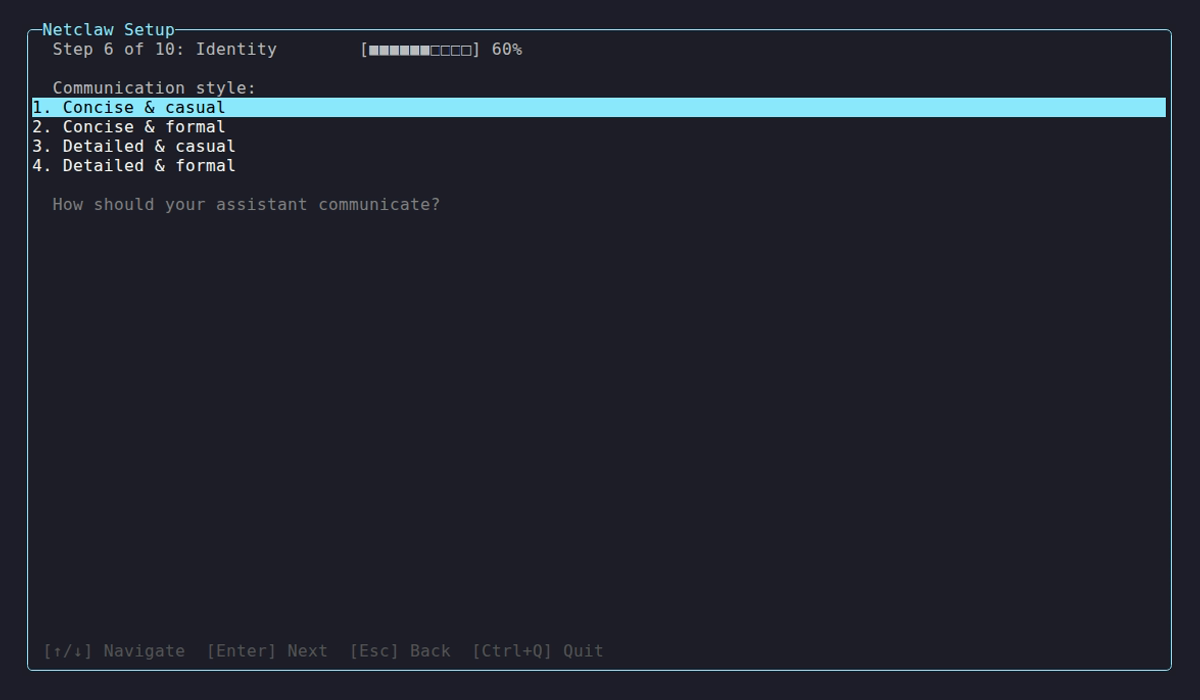

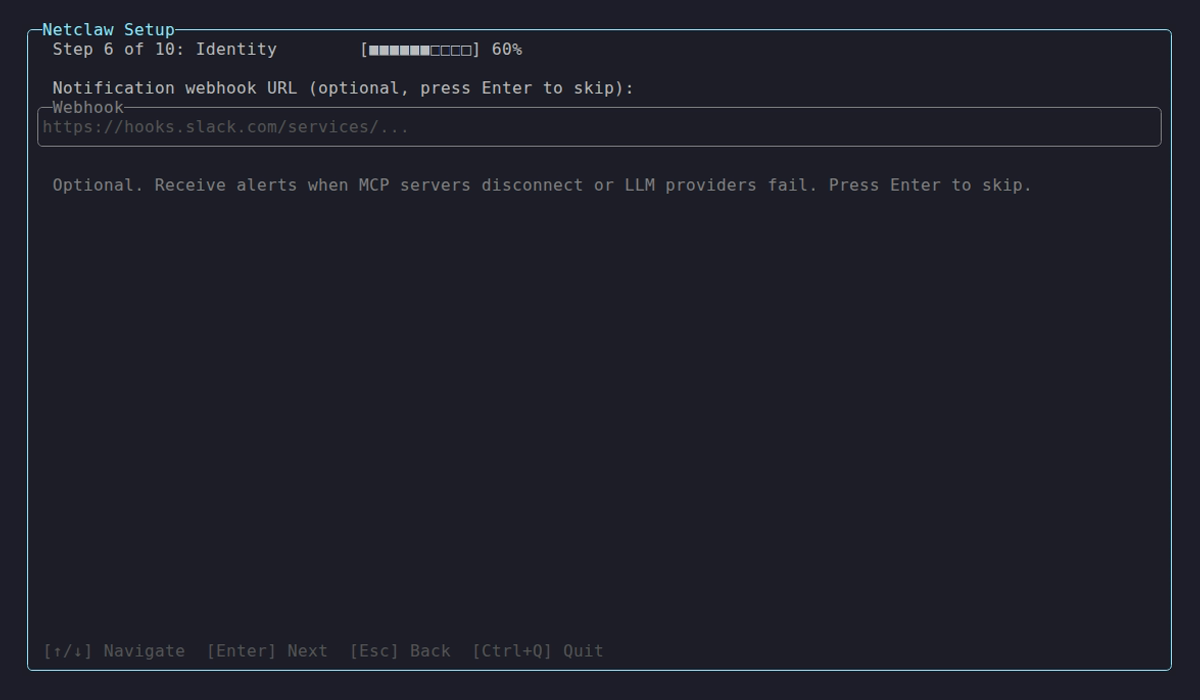

Give your agent a name, pick a personality style (shapes tone in chat), set a timezone for scheduling, and optionally wire up a webhook URL for outbound notifications. The screenshots walk you through each field.
8. External skills
Section titled “8. External skills”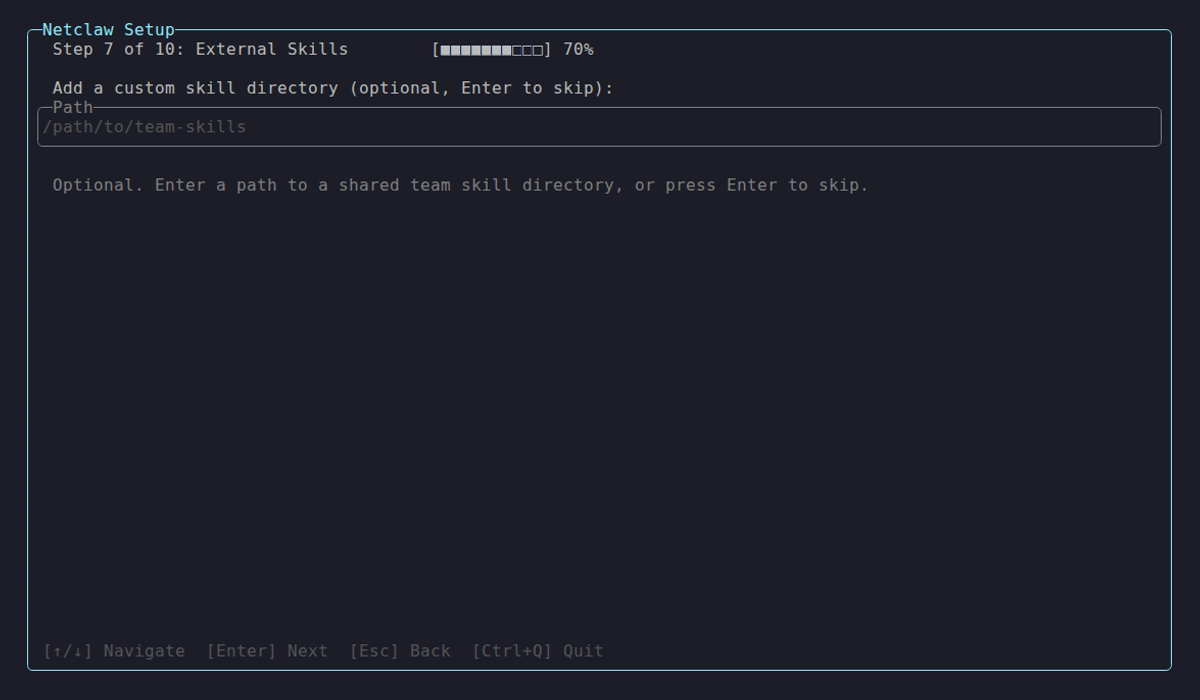
Point to a local directory with custom skill definitions.
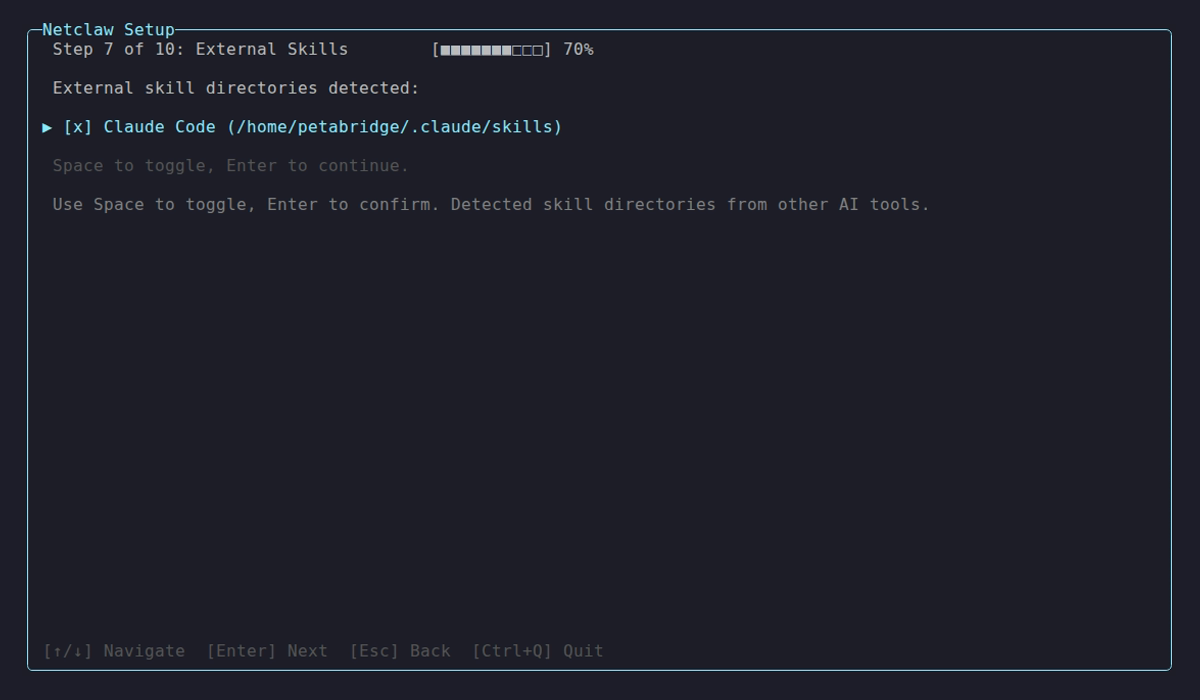
Add remote skill servers or additional skill packages.
9. Skill feeds
Section titled “9. Skill feeds”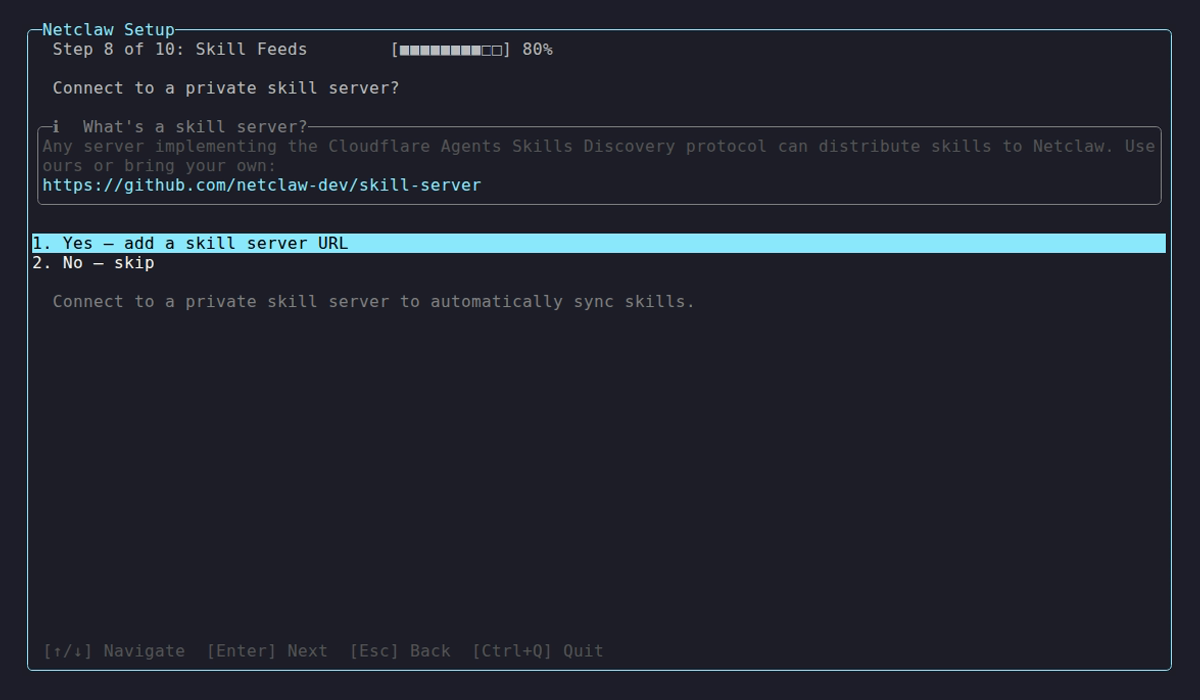
Subscribe to skill feeds — curated skill collections from the community or your org.
10. Network exposure
Section titled “10. Network exposure”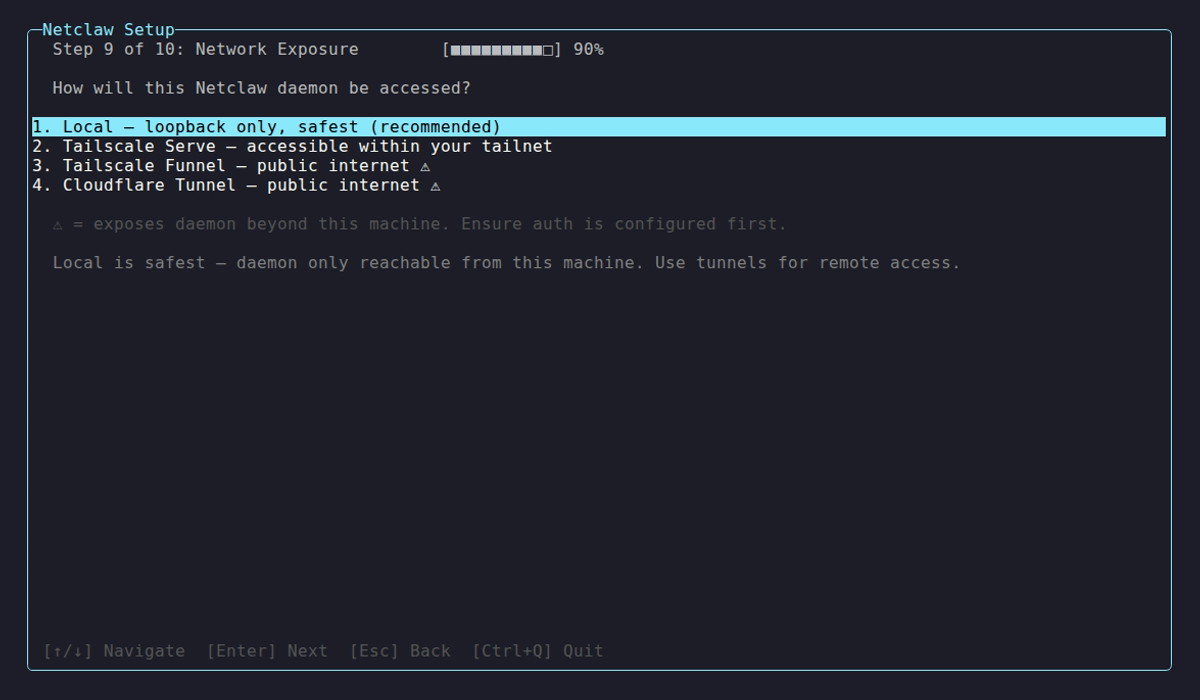
| Mode | Reachability | Requires |
|---|---|---|
local | Loopback only (this machine) | Nothing |
tailscale-serve | Your Tailscale tailnet | tailscaled running |
tailscale-funnel | Public internet via Tailscale | tailscaled running |
cloudflare-tunnel | Public internet via Cloudflare Tunnel | cloudflared running |
The internet-facing modes (tailscale-funnel, cloudflare-tunnel) make you type an explicit confirmation. They’re not kidding about the warning.
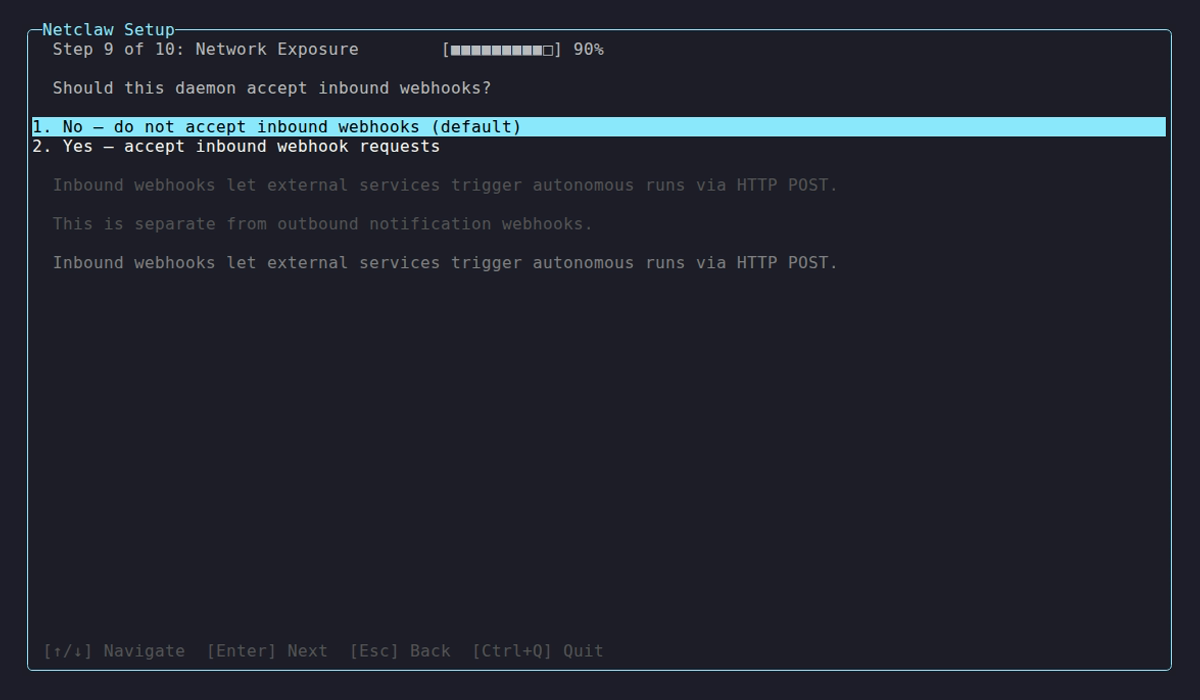
If you enabled webhooks, you’ll configure inbound routes here.
11. Health check
Section titled “11. Health check”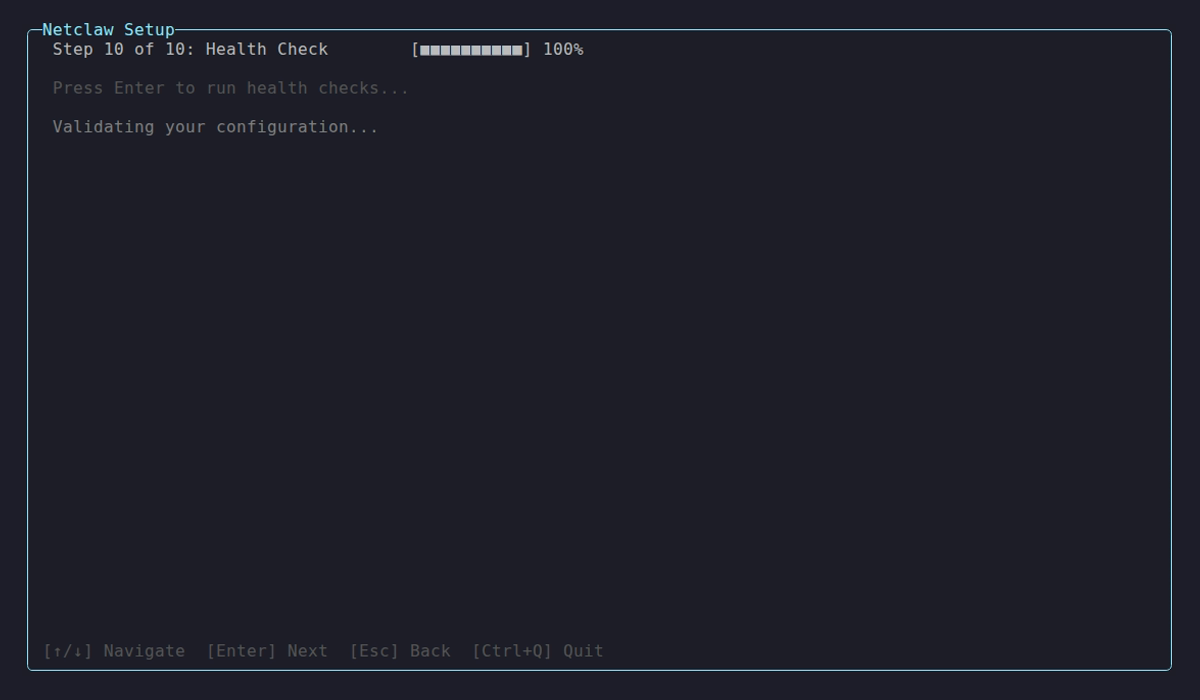
Validates config files, tests provider connectivity, verifies channel tokens, checks tunnel prerequisites.
All green? The daemon starts automatically.
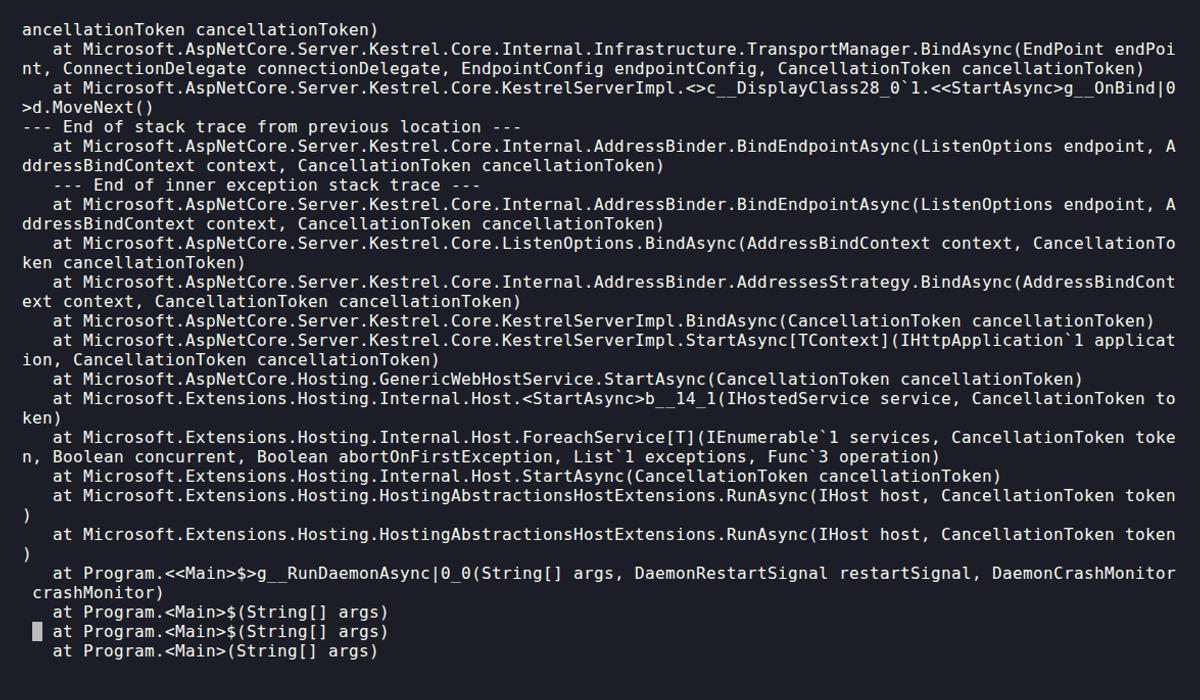
If something fails, the wizard tells you which check broke and suggests running netclaw doctor for detailed diagnostics.
What it creates
Section titled “What it creates”| File | Purpose |
|---|---|
~/.netclaw/config/netclaw.json | Main configuration (includes security posture) |
~/.netclaw/config/secrets.json | Encrypted credentials |
~/.netclaw/identity/ | Agent identity and personality |
After init
Section titled “After init”# Verify everything is healthynetclaw doctor
# Check daemon statusnetclaw status
# Start your first conversationnetclaw chatRelated commands
Section titled “Related commands”netclaw doctor— Diagnose config and connectivity issues post-setupnetclaw status— Check daemon health and connector statesnetclaw provider— Change or add providers without re-running initnetclaw model— Reassign model roles without re-running init
Resources
Section titled “Resources”- OpenRouter documentation — API keys, model catalog, rate limits
- Slack Socket Mode — How netclaw connects to Slack without a public endpoint
- Tailscale Funnel documentation — Exposing services to the public internet via Tailscale
- Cloudflare Tunnel documentation — Exposing services via Cloudflare’s network